Sponsored by Sophos
Sponsored by HelpSystems
Identity and Access Management for IBM i
Sponsored by HelpSystems
When Malware Attacks your IBM i, AIX or Linux Server: True Stories from the Field
Sponsored by Tata Communicatiions
Q4 2017 Security Transformation Study: Executive Report
Sponsored by VMware
Eight Common Pitfalls of App and Desktop Virtulization
Sponsored by VMware
Digital Workspace Basics
Sponsored by VMware
Enterprise Mobility Trends to Watch
Sponsored by Digital Guardian
A Practical Approach to GDPR Compliance
Sponsored by Digital Guardian
GDPR Compliance Requires Data Loss Prevention
Sponsored by Venafi
Dark Web Research: Criminals Pay Top Dollar for Your Certificates
Sponsored by BitSight
Cybersecurity Benchmarking: A CIO's guide for Reducing Security Anxiety
Sponsored by BitSight
Creating Efficiencies In Vendor Risk Management
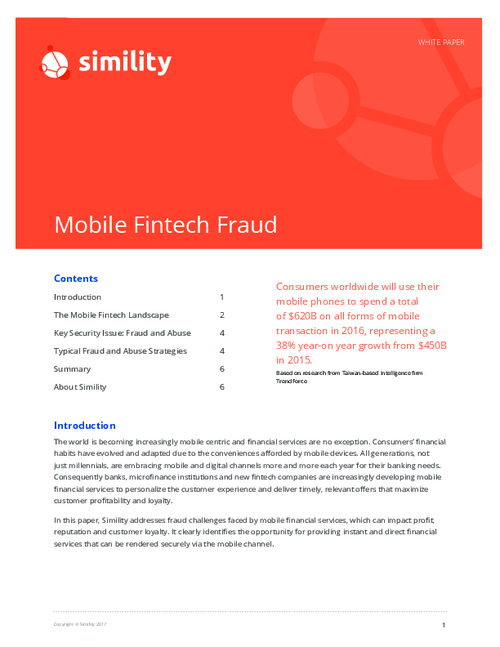
Sponsored by Simility
Mobile Fintech Fraud
Sponsored by IBM
Threat Intelligence Index 2017
Sponsored by IBM