Sponsored by BeyondTrust
Sponsored by AWS
Achieve Machine Learning Results Faster
Sponsored by Cyberark
Revisiting Ransomware Protection: An Assume-Breach Perspective
Sponsored by Splunk
The Essential Guide to Container Monitoring
Sponsored by Splunk
A Beginner's Guide to Kubernetes Monitoring
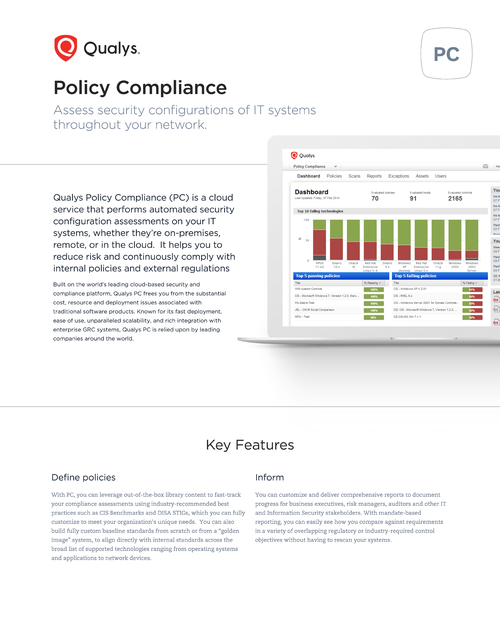
Sponsored by Qualys Inc.
Cloud Based Security & Policy Compliance
Sponsored by Silicon Labs
Preparing for Next-Generation Cyber Attacks on IoT
Sponsored by Nozomi Networks
The Leading Solution for OT & IoT Security and Visibility
Sponsored by Nozomi Networks
Integrating OT into IT/OT SOCs
Sponsored by Nozomi Networks
OT/IoT Security Report: Supply Chain and Persistent Ransomware Attacks Reach New Heights
Sponsored by Splunk
The 10 Essential Capabilities of a Best-of-Breed SOAR
Sponsored by Tessian
The State of Data Loss Prevention: Why DLP Has Failed and What the Future Looks Like
Sponsored by Palo Alto Networks
Take Your Endpoint Security to the Next Level
Sponsored by Palo Alto Networks
Cortex XDR - Breaking the Security Silos for Detection and Response
Sponsored by Palo Alto Networks