Sponsored by BitSight
Sponsored by LastPass
Four Distinct Topics Under Password Management
Sponsored by Carbon Black
Enterprise Guide to Hardening Endpoints Against Future Ransomware Attacks
Sponsored by Vasco
Behavioral Biometrics: Improve Security and the Customer Experience
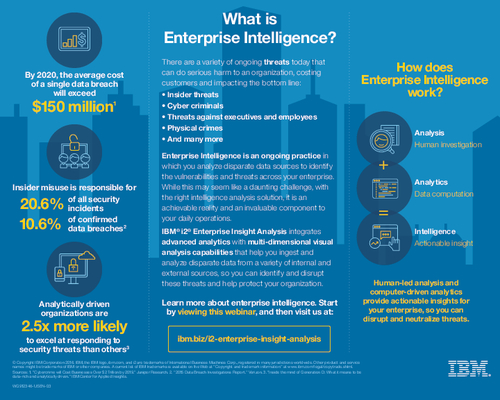
Sponsored by IBM
How Does Enterprise Intelligence Work?
Sponsored by IBM
Threat Intelligence Security Services Market Overview
Sponsored by IBM
Insider, Hacktivist or Nation State?
Sponsored by IBM
The Shortcomings of Current Fraud Prevention Approaches
Sponsored by BitSight
GDPR and Vendor Risk Management
Sponsored by LogRhythm
Simplify the the Federal OPSEC Mission with Security Intelligence
Sponsored by Palo Alto Networks
Top 10 Public Cloud Security Recommendations
Sponsored by Palo Alto Networks
Securing Traditional and Cloud-Based Data Centers with Next-Generation Firewalls
Sponsored by Palo Alto Networks
Guidelines for AWS Hybrid Cloud Deployments
Sponsored by Palo Alto Networks
Securely Enabling a Hybrid Cloud in Microsoft Azure
Sponsored by Harland Clarke