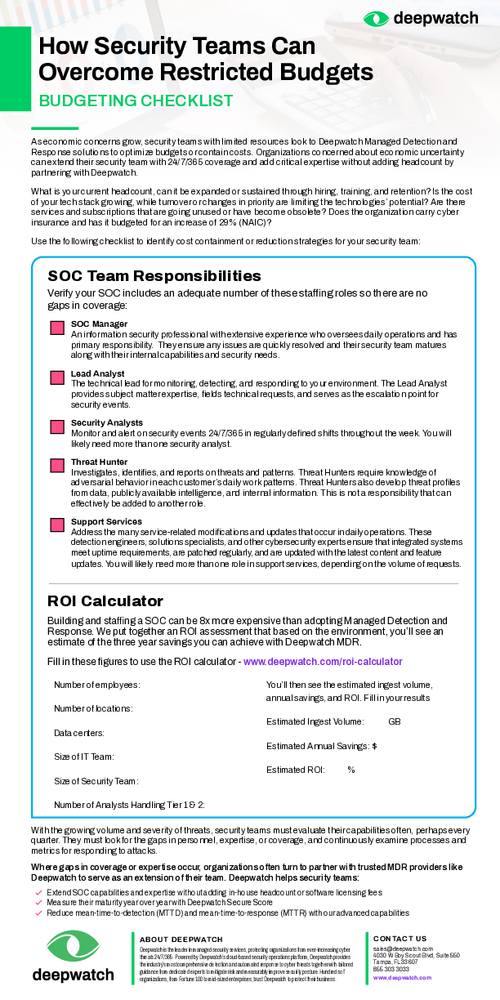
Sponsored by Deepwatch x Splunk
Sponsored by CrowdStrike
Adapt or Die: XDR Is On A Collision Course With SIEM And SOAR
Sponsored by Palo Alto Networks
Comprehensive and Proactive Security Operations for Financial Services
Sponsored by Splunk
Top 50 Security Threats
Sponsored by Splunk
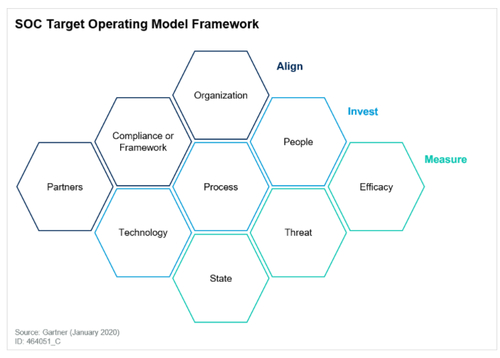
Gartner® Report: Create an SOC Target Operating Model to Drive Success
Sponsored by Graylog
What to Consider When Selecting a Source of Threat Intelligence
Sponsored by Splunk
Securing Complexity: DevSecOps in the Age of Containers
Sponsored by Nozomi Networks
Integrating OT into IT/OT SOCs
Sponsored by ServiceNow
ESG SOAR and MITRE ATT&CK
Sponsored by Splunk
The 10 Essential Capabilities of a Best-of-Breed SOAR
Sponsored by Splunk
The SOAR Buyer's Guide
Sponsored by Graylog
Leveraging a Highly Effective Combination of Human and Machine Power
Sponsored by IronNet
Data Sharing: Myths vs. Reality
Sponsored by Splunk
Measuring the ROI of Security Orchestration and Response Platforms
Sponsored by IronNet