Cybercrime , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development
Volusion Payment Platform Sites Hit by Attackers
Sesame Street Live Among Sites Hit by Card-Skimming Attacks, Researcher Warns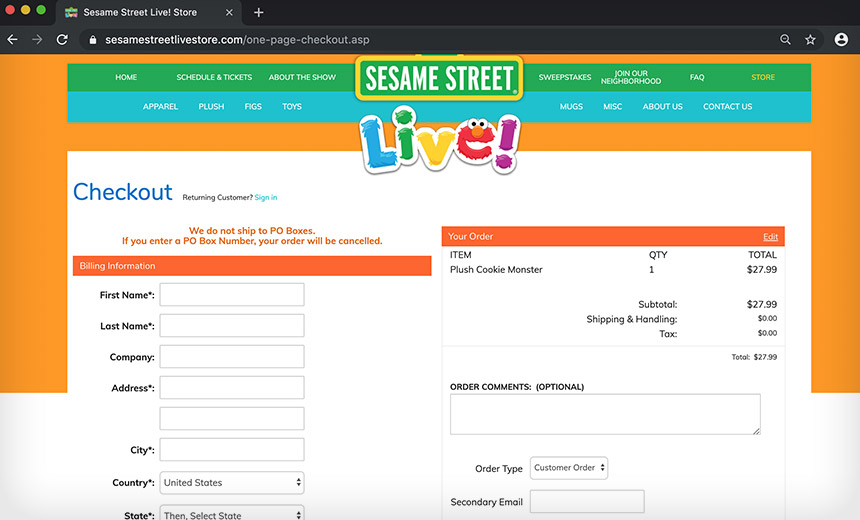
(Editor's Note: Story updated with response from Volusion.)
See Also: Panel Discussion | MITRE ATT&CK Framework: Seeing Through the Eyes of Your Attacker
A security researcher has uncovered credit card skimming attacks targeting websites that use a cloud-based payment platform from Volusion.
In a post on Medium, Marcel Afrahim, an endpoint security researcher at Check Point Software Technologies, says he found that attackers injected malicious JavaScript into the payment function for the Sesame Street Live online store to skim credit card and other payment data during the check-out process.
A further investigation found the same JavaScript on other sites that use the Volusion payment platform, the researcher says, without identifying those other sites. While it's not clear how many sites have been targeted, Afahim says about 6,600 payment sites use the payment platform.
And while it's not clear who is behind these attacks, the use of malicious JavaScript to skim credit card data is the hallmark of Magecart, an umbrella organization comprising a dozen groups that have been attacking the e-commerce sites of several major companies - including British Airways, Ticketmaster and Newegg - over the last 18 months (see: Magecart Group Continues Targeting E-Commerce Sites).
"The most obvious threat actor that is currently famous for card skimming and compromising … e-commerce websites is Magecart, which has the history of using Vultr Holdings data centers (just live Volusion-Cdn[.]com) and using public cloud storage to host their malicious scripts," Afahim says.
Afahim discovered the attack against the check-out site for Sesame Street Live this week, although these incidents could have started as far back as Sept. 12. The payment function for the Sesame Street Live online store remained offline Wednesday.
On Thursday, a spokesperson for Volusion told Information Security Media Group that the attacks had been stopped within a few hours of the company being notified, but that an investigation was still underway.
"A limited portion of customer information was compromised from a subset of our merchants. This included credit card information, but not other associated personally identifying details. We are not aware of any fraudulent activity connected to this matter," the spokesperson says. "Volusion has taken action to help secure accounts, and we are continuing to monitor this matter in order to assure the security of our merchants."
Trend Micro researchers are also looking into these incidents
@Volusion Hi! We sent you a Direct Message. Looking forward to your reply.
— Trend Micro Research (@TrendMicroRSRCH) October 7, 2019
Stealing Credit Card Data
While credit card skimmers generally have relied on hardware installed at the point of sale or in ATMs, the used on malicious JavaScript to skim credit cards from payment sites is a much more lucrative approach.
These types of virtual skimmers, referred to as JavaScript skimmers, JavaScript sniffers or JS sniffers, can be cheaply purchased on underground sites. In most cases, the attackers target the check-out and payment pages of online retail sites (see: Surge in JavaScript Sniffing Attacks Continues).
This malicious code is proficient at sweeping up payment card data, including name, card number, expiration date and CVV information, researchers say.
In the incidents that Afahim uncovered, the malicious JavaScript appears to have uploaded to a cloud storage service called storage.googleapis.com. Volusion is a Google cloud customer.
Afrahim says he found unusual JavaScript in a cloud-based storage bucket named "volusionapi" on the Sesame Street Llive site.
"So it seems to be a bit odd that of all the pages on the site, there is an external [JavaScript] being loaded from some randomly named storage on the checkout page of an e-commerce website," Afahim says.
The malicious JavaScript is fairly simple. One part is designed to read data types into the fields of a payment site, Afahim notes. Another part stores that data in a temporary storage file in a web browser before it's sent back to the attackers, he reports.
During his investigation, Afahim found that many of the files used to deliver or house the malicious JavaScript had innocuous or plain-sounding names to disguise their activity. In some cases, these files looked like normal web analytics files.
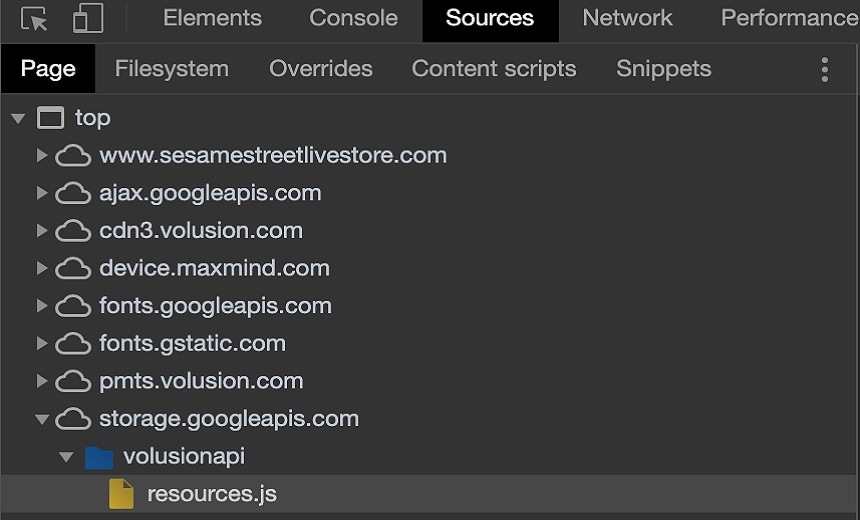
In addition, planting the JavaScript in the Google cloud storage platform that Volusion uses enables the attackers to spread the JavaScript to many of payment sites built on the Volusion's platform, Afahim says.
"The compromise is not unique to Sesame Street store, and most likely any e-commerce website hosted on Volusion is probably running malicious code and posting the credit card info of the consumers to the outsider domain," Afahim says.
Magecart on the Rise
In previous research, security firm RiskIQ found that Magecart groups have attempted to inject their own malicious JavaScript into unsecured Amazon Web Service's S3 cloud storage buckets (see: RiskIQ: Magecart Group Targeting Unsecured AWS S3 Buckets).
Over the past year, RiskIQ has detected Magecart-linked code over 2 million times and over 18,000 domains have been breached as a result.
RiskIQ researchers declined to comment on the attacks targeting Volusion. But Jordan Herman, a threat researcher with the firm, previously told Information Security Media Group that Magecart typically targets small firms in order to access the payment details of customers shopping with much larger companies.
"We see this in the focus of some groups on attacking small third-party vendors as a means to gain access to larger, better-resourced organizations," Herman says. "Many websites, big ones included but especially small ones, have little visibility into JavaScript running on their sites and make easy targets for Magecart actors. As we mentioned in the report, these skimmers stay on a site for an average of over three weeks, which means every visitor that made a purchase on their site in that time could have been victimized."