Account Takeover Fraud , Card Not Present Fraud , Cybercrime
Russia Shutters 3 Carding Markets, Including Trump's Dumps
Recently Disrupted Marketplaces Accounted for 50% of Carder Sales, Researchers Say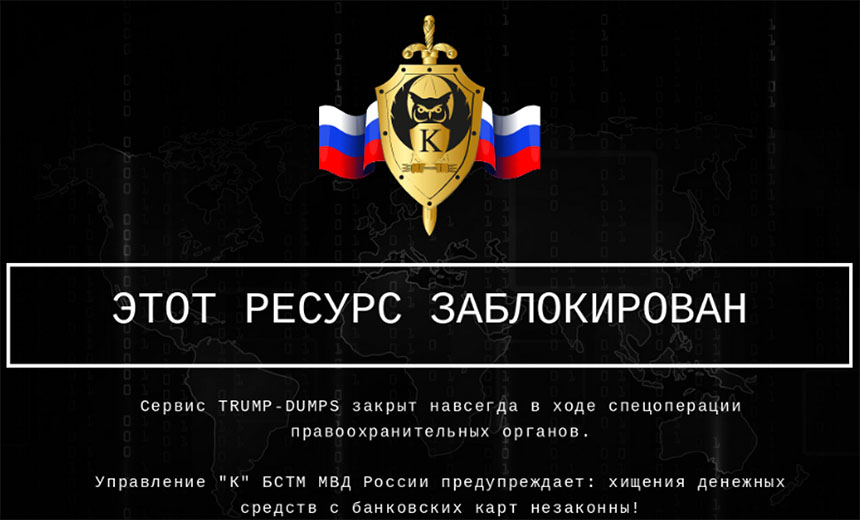
Russian authorities have continued to arrest alleged administrators of multiple Russian-language cybercrime markets and communities. It's not clear if the arrests are being made as part of any Moscow-ordered crackdown in response to demands by the White House that Russia better disrupt cybercriminals hitting foreign targets from inside the country's borders.
See Also: OnDemand | Payments Without Borders: Prevent Fraud and Improve the Customer Experience
But earlier this month Ferum Shop and Sky-Fraud went dark, and their homepages were replaced by takedown notices posted by the Russian government's Ministry of Internal Affairs' Department K, which focuses on technology crime, says threat intelligence firm Flashpoint.
Another shop for stolen payment card data, called Trump's Dumps, aka TDStore, has also recently been shuttered, as has Ultimate Anonymity Services, or UAS, which specialized in selling remote desktop credentials, Flashpoint says. So-called carder or carding markets, among other activities, sell "dumps," by which they mean the data stored on payment card magnetic stripes, which is typically stolen via point-of-sale devices.

Security researchers say that a message - "Which one of you is next?" - had been added in the form of an HTML comment to the sites' homepages, together with an emoji of a police officer.
In what appears to be related news, Russian news agency Tass reported last week that six individuals were arrested for violating Article 187 of Russia's criminal code, which among other provisions includes a prohibition on buying or selling stolen payment card data.
The suspects were arrested in different areas of Russia, Tass reports, naming the suspects as: "Denis Pachevsky, general director of Saratovfilm Film Company LLC; Alexander Kovalev, an individual entrepreneur; Artem Bystrykh, an employee of Transtechcom LLC; Artem Zaitsev, an employee of Get-net LLC; and two unemployed people, Vladislav Gilev and Yaroslav Solovyov."
Artem Alexeyevich Zaytsev is "CEO of Get-Net LLC, which is the registrar of the domains of Sky-Fraud, Trump's Dumps, UAS and Ferum, as well as several other domains, some of which look like legitimate businesses," Flashpoint says, noting that he appears to have been running sites since 2008. It says Alexandra Kovaleva is the majority shareholder of Get-Net.

The takedown notice from Department K includes a warning that the "theft of funds from bank cards is illegal." Article 187, which concerns the illegal circulation of means of payment, specifically prohibits the production, acquisition, storage or transport of counterfeit payment cards, or the use of "electronic means," including software "intended for illegal acceptance, issuance, transfer of funds," according to a translation published by Flashpoint.
Violating Article 187 can lead to a prison sentence of up to seven years.
It's not clear if any of the shuttered markets might have listed for sale payment data stolen from Russian banks. Russian-language cybercrime sites typically ban any activities, including bank fraud, ransomware or malware, that target Russia or friendly, neighboring countries (see: Russia's Cybercrime Rule Reminder: Never Hack Russians).
Follows UniCC and Luxsocks Disruption
The takedowns of Ferum Shop, Sky-Fraud, Trump's Dumps and UAS follow the takedown of carding site UniCC last month, together with affiliated site Luxsocks. Tass first reported at the time that Russia's Federal Security Service, the FSB, arrested the market's alleged administrator, Andrey Sergeevich Novak, and placed three alleged criminal hacking accomplices under house arrest.
All four suspects have been accused of being part of the Infraud Organization, and of violating not just Article 187 of the criminal code but also Article 272, which involves illegal access to computer information, Tass reports.
Novak is also wanted by U.S. authorities. A federal indictment unsealed in 2018 charges him with being an alleged founder of the Infraud Organization, a financially focused cybercrime syndicate disrupted that year. Prosecutors have tied Infraud to $530 million in losses.
As Russia never extradites its citizens, he is unlikely to ever appear before a U.S. judge, so long as he doesn't leave Russia.
Cybercrime Market Economics
Demand for carding sites has long remained robust, and established players and newcomers alike continue to compete for market share. For example, after the world's biggest carding site, Joker's Stash, closed up shop in January 2021, UniCC seized its mantle, security experts say (see: Darknet Markets Compete to Replace Joker's Stash).
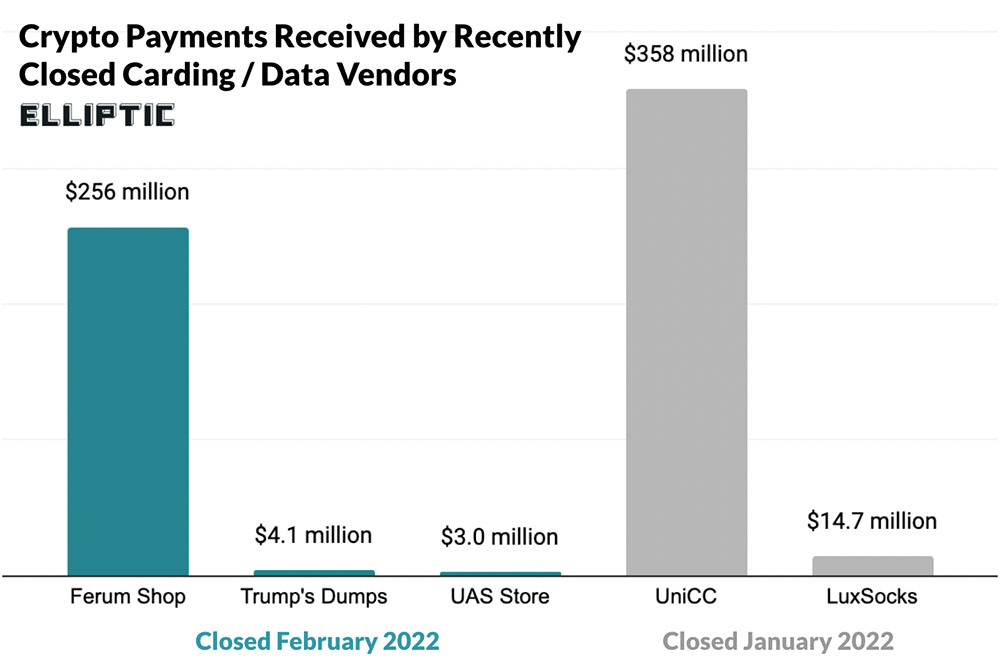
After UniCC was disrupted last month, Ferum Shop - already active for five years - briefly became the world's most popular carding market, says blockchain analysis firm Elliptic.
Carding markets remain a fixture of the cybercrime underground, as the recently shuttered sites highlight. "Hundreds of millions of payment card details have been stolen from online retailers, banks and payments companies before being sold for crypto assets on online marketplaces such as Ferum Shop or Trump's Dumps," Elliptic says. "These stolen cards have value because they can be used to purchase expensive items or gift cards, which can then be resold for cash." This process - known as carding - can be used to generate profits outright, as well as to launder or cash out stolen funds, it says.
Sky-Fraud had been active for about four years, and "was never considered to be a high- or even mid-tier forum, but Sky-Fraud was a major source for beginner carders and cybercriminals," Flashpoint says.
The carding markets that have been recently shut accounted for about 50% of all carding sales, Elliptic says.
UAS, meanwhile, sold stolen or brute-forced RDP credentials, which remain one of the dominant tactics used by attackers to gain initial access to a corporate network (see: Ransomware Gangs' Not-So-Secret Attack Vector: RDP Exploits). From there, the attackers can map the network, steal sensitive data and potentially unleash ransomware.
As individual markets go, UAS earned relatively low profits. "Active since November 2017, UAS made around $3 million in cryptocurrency proceeds, of which $862,000 was made during the pandemic," Elliptic says. "The site also sold access to proxies, which allowed criminals to further anonymize their web usage."
Arrests Causing Criminal Panic
But carding and RDP markets are not the only types of cybercrime to have been recently targeted by Russian authorities.
Last month, the FSB arrested 14 individuals suspected of working with the REvil - aka Sodinokibi - ransomware operation.
The increased tempo of cybercrime arrests in Russia hasn't gone unnoticed by criminals. Indeed, the recent takedowns have "led to speculation on top-tier forums that Russian security agencies may cooperate with Western law enforcement on certain arrests," Flashpoint says. "This potential cooperation could change the cybercrime landscape and limit the available venues where threat actors can communicate, or buy or sell illicit goods."