Application Security , Cybercrime , Fraud Management & Cybercrime
New Ursnif Variant Spreads Through Infected Word Documents
Banking Trojan Designed to Steal Passwords and Credentials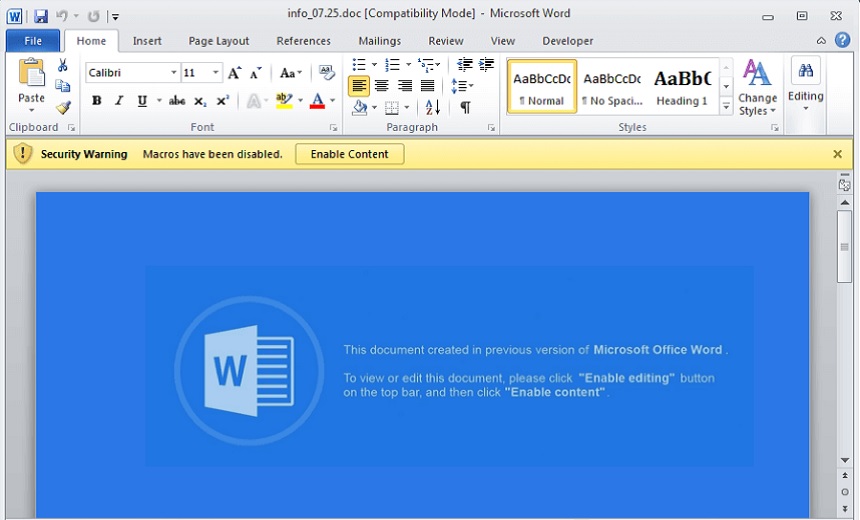
A new variant of the Ursnif Trojan is targeting vulnerable systems in an attempt to steal banking passwords and other credentials. The malware is spreading through infected Microsoft Word documents, and it has the ability to evade advanced security filters, according to researchers at Fortinet.
See Also: Bank on Seeing More Targeted Attacks on Financial Services
Ursnif has been around in some form for about 10 years and has grown more popular over that time. The latest variant appears to have been compiled around July 26 and is spreading through phishing emails that contain malicious Word documents, Fortinet researchers note in a blog. The file, which was identified as "info_[date].doc," has been actively spreading over the last month, the researchers say.
"This threat is actively spreading," Xiaopeng Zhang, a researcher with Fortinet, notes in the blog. "During my analysis, which started with just a few samples, the volume of captured samples and the number of triggers this new variant set off in our global network of sensors kept growing."
Although the number of systems that have been infected by the updated Ursnif variant remains unclear, the Fortinet researchers say that they have gathered several infected Word documents samples from across the world and are now warning organizations to be on the alert for this new strain.
Evading Detection
To activate its malicious payload, the updated version of the Ursnif Trojan prompts a false message requesting that the user "enable content," claiming that the malicious file only runs in a previous version of the Word and that they need to enable macros in order to view it, according to Fortinet.
After the set of macro permissions is granted, the malware launches a malicious Visual Basic for Applications code, which then downloads the main payload to the victim's computer, the researchers note.
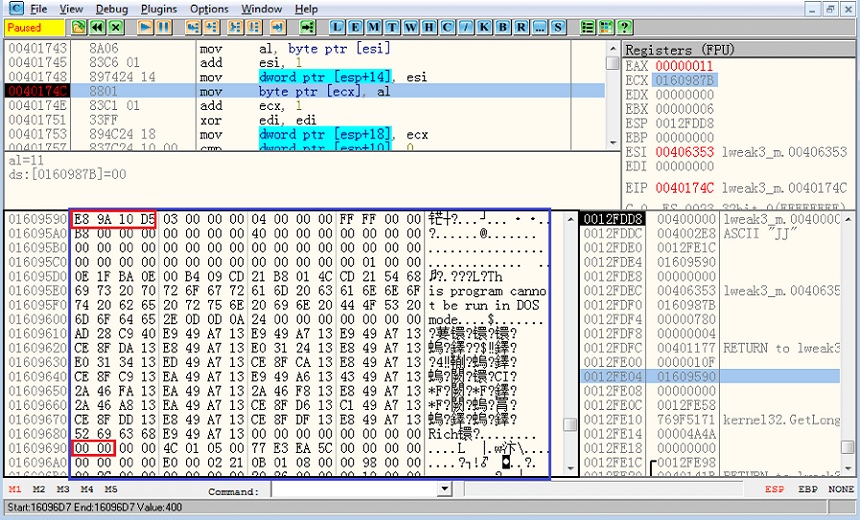
Following its installation, the malware generates several “iexplore.exe” processes that appear and disappear. It's through this process that the malware sends out the data it has collected from the infected system back to the attacker's command-and-control server, the researchers say.
To help evade detection, the malware's command-and-control server contains a reference list of security companies, such as Microsoft and Avast. "In fact, this is a way to deceive researchers who capture and analyze the traffic," the researchers report.
Ursnif Variants
Over the past 10 years, variants of the Ursinf Trojan have been involved in high-profile attacks against banks and another financial institutions. The source code for the malware leaked online in 2015, which enabled attackers to develop more customized and harder-to-detect versions of the Trojan.
Ursinf, which also goes by the names Dreambot and Gozi ISFB, is designed to steal passwords and credentials from victims - with a particular focus on the banking and financial sectors - and has proven to be effective at this task.
For instance, in March, security researchers at Cybereason discovered a variant of the Ursnif malware that targeted Japanese-speaking bank customers. The attackers sent a phishing campaign with an infected Microsoft Excel sheet and exploited the "enable edit" features to activate the malware. Once successfully installed, the Trojan was capable of stealing email configurations and other user credentials (see: Ursnif Banking Trojan Variant Steals More Than Financial Data ).
In another example from 2016, a hybrid of the Trojan called GozNym was used to steal nearly $4 million from banks, credit unions and e-commerce sites in the U.S. and Canada. The strain, which was created from a combination of the Nymaim and Gozi ISFB malware, could steal financial data and take screen captures, sending this data back to the attackers who then attempt to transfer the money from the victims' bank account (see: New Hybrid Banking Trojan 'GozNym' Steals Millions ).