Hardware / Chip-level Security
Microsoft Offers Payouts for New Spectre, Meltdown Flaws
Bug Bounty Program Seeks to Avoid Further Speculative Execution Unpleasantness
To help identify and mitigate the next generation of Spectre and Meltdown flaws, technology giants are putting their money where their mouth is.
See Also: Identity as a Game-Changing Breach Defense
Microsoft, following a similar move by Intel, has announced that until the end of this year, it will be offering bug bounties of up to $250,000 for information leading to the successful identification of speculative execution attacks (see Expect More Cybersecurity 'Meltdowns').
Speculative execution refers to a CPU optimization technique that's widely used in modern processors. But the functionality, which is physically built into processors, can be targeted via a trio of "side-channel attacks" to trigger information leaks.
Millions of processors built by Intel, AMD and ARM are vulnerable to variant 1 of these flaws, which is a bounds check bypass (CVE-2017-5753) known as Spectre, and variant 2, a branch target injection (CVE-2017-5715) also known as Spectre. Many Intel processors, as well as some built by ARM, are vulnerable to variant 3, which is a rogue data cache load (CVE-2017-5754) known as Meltdown.
Although attacks exploiting the flaws are not necessarily simple, they could be used to recover passwords, encryption keys and other data in memory.
"Speculative execution is truly a new class of vulnerabilities, and we expect that research is already underway exploring new attack methods," Phillip Misner, principal security group manager for Microsoft Security Response Center, says in a blog post.
Microsoft's speculative execution bounty program focuses has four tiers. Tier one "focuses on new categories of attacks involving speculative execution side channels," Misner says. Tiers two and three, meanwhile, "focus on identifying possible bypasses for mitigations that have been added to Windows and Azure to defend against the attacks that have been identified." Finally, the fourth tier "covers exploitable instances of CVE-2017-5753 or CVE-2017-5715" - the official designations for the Spectre flaws - "that may exist."
Microsoft's Speculative Execution Bug Bounties
Misner promised that Microsoft will share any vulnerability information it receives with the relevant organizations via coordinated vulnerability disclosure. "Together with security researchers, we can build a more secure environment for customers," he says.
To help researchers understand what's known about these flaws, Microsoft's security research and defense team on Thursday published a detailed blog post "describing how we investigated this new vulnerability class, the taxonomy we established for reasoning about it and the mitigations we have implemented as a result."
AMD Flaws
Microsoft's call for coordinated vulnerability disclosures - rather than simply releasing news of flaws publicly with little warning beforehand to vendors or manufacturers - came on the heels of Israeli startup CTS last week launching a website called AMD Flaws and releasing a "Severe Security Advisory on AMD Processors" white paper that says there are 13 serious security flaws in AMD's Zen processors, including EPYC, Ryzen, Ryzen Pro and Ryzen Mobile (see AMD Chipset Flaws Are Real, But Experts Question Disclosure).
Technical details of the flaws have not been publicly released. To be clear, none appear to be speculative execution attacks. Still, CTS has been widely criticized for engaging in what many allege was at best a PR stunt.
Defending his company's move, CTS's CFO, Yaron Luk-Zilberman, said in an interview with AnandTech that rather than wait until AMD had come up with mitigations, which CTS estimated could take a year, the company opted to issue public warnings.
His company also said in notes accompanying its disclosure: "We may have, either directly or indirectly, an economic interest in the performance of the securities of the companies whose products are the subject of our reports."
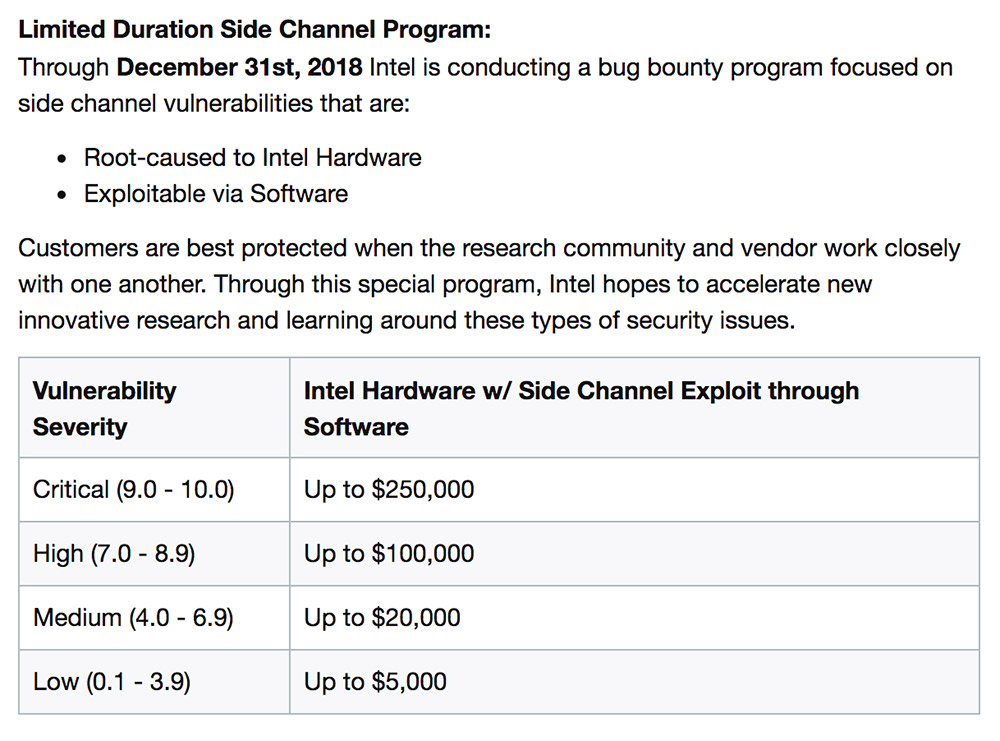
Intel Bug Bounty: Up to $250,000
Microsoft isn't the first technology giant to offer researchers cold, hard cash in exchange for their speculative execution identification and eradication findings, offered up for a nonpublic, coordinated fixing effort.
Last month, in the face of accusations that it's downplayed the extent and severity of the speculative execution flaws in its CPUs, Intel announced that it was expanding its existing bug bounty program, launched in March 2017 via HackerOne, so that it would no longer be invitation-only (see Intel Faces 32 Spectre/Meltdown Lawsuits).
Until the end of 2018, Intel says it is running "a new program focused specifically on side channel vulnerabilities" with a maximum reward of $250,000. Small print: The vulnerability must be "root-caused to Intel hardware," meaning it doesn't occur in third-party hardware, and must also be "exploitable via software."
Intel's Side-Channel Vulnerability Bug Bounties
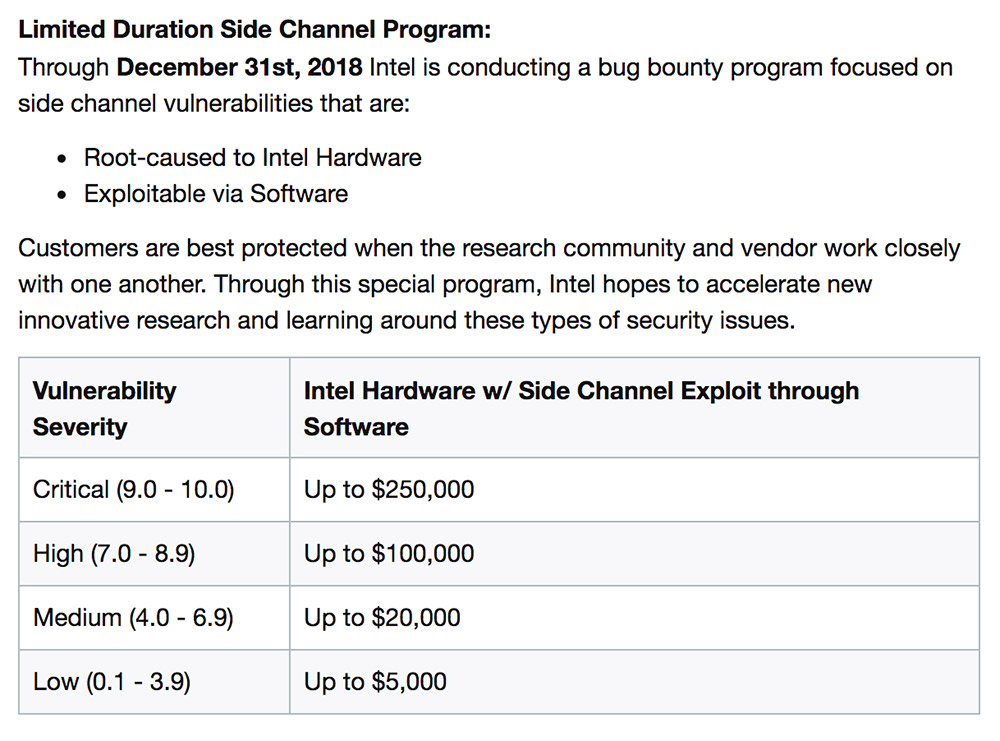
Among other terms and conditions, "recent acquisitions by Intel are out of scope for the bug bounty program for a minimum period of six months after the acquisition is complete."
Intel says it's also raised its maximum reward for other flaws found by researchers in its wares to $100,000.
"Coordinated disclosure is widely regarded as the best way to responsibly protect customers from security exploits," Rick Echevarria, general manager of platform security at Intel, said in a blog post. "It minimizes the risk that exploitable information becomes publicly known before mitigations are available. Working closely with our industry partners and our customers, we encourage responsible and coordinated disclosure to improve the likelihood that users will have solutions available when security issues are first published."
Intel Hits Microcode Milestone
Meanwhile, Spectre and Meltdown patching efforts and fixes proceed (see Performance Hit: Meltdown and Spectre Patches Slow Systems).
Apple, Cisco, Dell, Fujitsu, Google, IBM, Juniper, Microsoft and Oracle are among the many vendors that must update users' firmware and operating systems with Meltdown and Spectre protections.
"Windows devices need both software and firmware updates to help protect them against these new vulnerabilities," Microsoft says.
Unfortunately, early efforts to fix the problem have had widespread system performance impacts (see Performance Hit: Meltdown and Spectre Patches Slow Systems).
Intel has also struggled to prepare and issue microcode updates since it was first informed of the flaws by Google researchers on June 1, 2017. Earlier this month, Microsoft said it would continue to issue those updates directly to its users, as Intel released them for different chipsets.
But last week, Intel announced that it had reached a milestone.
"We have now released microcode updates for 100 percent of Intel products launched in the past five years that require protection against the side-channel method vulnerabilities discovered by Google," Intel CEO Brian Krzanich announced in a Thursday blog post.
Intel Previews 'Partitioning'
Krzanich says Intel has continued to research ways to block these flaws. "While variant 1 will continue to be addressed via software mitigations, we are making changes to our hardware design to further address the other two," he says. "We have redesigned parts of the processor to introduce new levels of protection through partitioning that will protect against both variants 2 and 3."
While details of how this partitioning will work have yet to be released, Krzanich likens the approach to adding "additional 'protective walls' between applications and user-privilege levels to create an obstacle for bad actors."
He says the processor changes will begin to hit the market in the second half of this year via Intel's next-generation Xeon Scalable processors, code named Cascade Lake, as well as via new versions of Intel's 8th generation Core processors.













