Cybercrime , Cyberwarfare / Nation-State Attacks , Forensics
Microsoft Finds Backdoor; CISA Warns of New Attack Vectors
Devastating Scope of Hacking Campaign Expands
Microsoft says it has removed malware related to an expansive hacking campaign that has ensnared thousands of organizations and U.S. government agencies.
See Also: The State of Organizations' Security Posture as of Q1 2018
Microsoft’s disclosure comes as the devastating scope of the campaign grew on Thursday, with a fresh U.S. government warning that the recently discovered supply chain compromise may not be the only way a hacking group is infiltrating organizations.
Microsoft says it found malicious binaries that came from SolarWinds, the Austin-based company whose software supply chain was infiltrated by a hacking group.
Reuters, which was first to report Microsoft was affected, says that Microsoft “also had its own products leveraged to further the attacks on others,” citing anonymous sources.
Microsoft, however, says “we believe the sources for the Reuters report are misinformed or misinterpreting their information.”
”We have not found evidence of access to production services or customer data,” according to a Microsoft statement. “Our investigations, which are ongoing, have found absolutely no indications that our systems were used to attack others.”
Nonetheless, Microsoft marks a significant and worrisome addition to a growing list of victims. Most organizations use some kind of Microsoft software, and a successful attack on its supply chain could exponentially expand the range of organizations affected. At least so far, that doesn’t appear to have occurred.
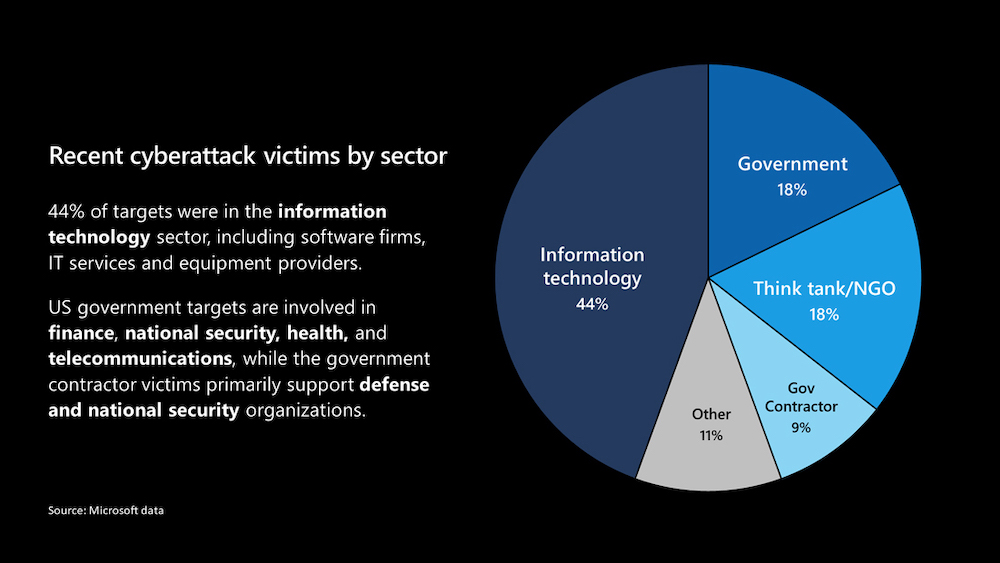
Microsoft has identified 40 of its customers that were targeted “more precisely” by the group, writes Brad Smith, the company’s president. Those customers downloaded the malicious SolarWinds updates and were “compromised through additional and sophisticated measures,” he writes.
About 80% of those victims are in the U.S., with others in Canada, Mexico, Belgium, Spain, the U.K, Israel and UAE, Smith writes. The victims include government agencies, security and technology firms and nongovernmental organizations.
“It’s certain that the number and location of victims will keep growing,” Smith writes. “The attack unfortunately represents a broad and successful espionage-based assault on both the confidential information of the U.S. government and the tech tools used by firms to protect them.”
Politico reported on Wednesday that the Department of Energy and the National Nuclear Security Administration, which maintains the nation's nuclear weapons, were also targeted.
CISA: SolarWinds Not Only Infection Vector
The hacking campaign involved slipping malicious backdoors into software updates for SolarWinds’ popular network management software called Orion. Once those updates were installed by organizations, the attackers had free-ranging access to networks and could install other malware and access data, such as email accounts.
Orion has powerful, administrative access, says John Bambenek, chief forensic examiner and president of Bambenek Consulting and an incident handler at the SANS Institute.

”Owning SolarWinds is effectively owning the CIO,” Bambenek says. “You’ve got the infrastructure. You don’t need a special tool to sit there and change passwords or create accounts or spin up new VMs [virtual machines]. It’s all built in, and you’ve got full access.”
As many as 18,000 organizations downloaded the infected updates, SolarWinds has said. But experts believe the hacking group likely only deeply penetrated a few dozen organizations, with many in the U.S. government sphere.
The U.S. Cybersecurity and Infrastructure Security Agency warned Thursday, however, that the SolarWinds compromise “is not the only initial infection vector this actor leveraged.”
CISA’s alert says that it's investigating some incidents in which victims either didn’t use the Orion software or, if it was present, there were no signs of exploitation activity.
ACTIVITY ALERT
— US-CERT (@USCERT_gov) December 17, 2020
Review @CISAgov’s new Alert on the #APT campaign against federal agencies & critical infrastructure, providing updated affected product versions, IOCs, ATT&CK® techniques, and mitigation steps. https://t.co/ZgzAbUNKjL #Cyber #Cybersecurity #Infosec pic.twitter.com/QnntuVhUXb
CISA notes the incident response firm Volexity has found tactics, techniques and procedures used against SolarWinds that are associated with other vectors.
Starting last year, Volexity investigated three intrusions at an unidentified U.S. think tank, where it noticed the attack group used a variety of refined tricks to stay in the network. It wrote an in-depth blog post about the incidents. Volexity concluded in hindsight that the last one was related to SolarWinds.
In one clever trick, Volexity says, the hacking group used a secret key that it previously stole to generate a cookie to bypass the Duo multifactor authentication protecting access to the Outlook Web app.
CISA notes in its alert that, in two of the intrusions against the think tank, there were initial access vectors “beyond SolarWinds Orion, and there may still be others that are not yet known.”
Volexity found the hacking group showed a strong interest in accessing the email systems of its victims, which is where it is advising clients to check for suspicious activity (see: SolarWinds: The Hunt to Figure Out Who Was Breached).
Attack Group is ‘Highly Capable’
Charles Carmakal, senior vice president and CTO of FireEye’s Mandiant forensics unit, says the advanced persistent threat group behind the compromises is “highly capable.”

Mandiant suspects the group uses multiple techniques to break into organizations, and CISA’s warning fits in with the resourceful nature of the group, he says. FireEye disclosed it was breached on Dec. 8, later connecting the breach to SolarWinds.
“They [threat actors] clearly have the capabilities and resources to have more than a single way to break into organizations,” Carmakal says.
Multiple software companies have been affected by the group, although it is undetermined yet if the software supply chains of those companies have been compromised, Carmakal says. Some were infiltrated via the SolarWinds compromise, but for others, the initial point of entry isn’t clear yet, he says.
“Several software companies and different types of organizations are trying to assess the impact of this campaign,” Carmakal says. “There is a lot of investigative work that is being done now.”
CISA says that, in addition to federal agencies, this hacking campaign poses a threat to state, local, tribal and territorial governments as well as critical infrastructure entities and other private sector organizations.
Other victims include the U.S. Commerce, Homeland Security, State and Treasury departments as well as the National Institutes of Health. In the private sector, Intel and Cisco have been affected (see: SolarWinds Supply Chain Hit: Victims Include Cisco, Intel).
More details will likely trickle out, says Rick Holland, CISO of security firm Digital Shadows and a former Army intelligence analyst. “However, the general public is unlikely to ever know the complete scope and implications of these intrusions,” he says.
Russian Involvement?
CISA’s alert does not identify the nation where the APT group is based. But one suspect is APT 29, also known as Cozy Bear, which is believed to be linked to Russia’s SVR foreign intelligence service. The group has been blamed for high-profile intrusions, including one against the Democratic National Committee in 2016.
The Russian government denies it is responsible (see: SolarWinds Supply Chain Hit: Victims Include Cisco, Intel).
The intrusion campaign likely started around March and ran through October, leaving a wide gap in which organizations could have been spied upon. It has raised questions about why the attackers weren’t detected sooner.
On Wednesday, The New York Times reported that the Department of Homeland Security's intrusion detection system, known as Einstein, failed to detect the attack against government agencies.
President-elect Joe Biden issued a statement pledging to make dealing with the SolarWinds-related breach and cybersecurity in general a top priority for his administration.
"We will elevate cybersecurity as an imperative across the government, further strengthen partnerships with the private sector, and expand our investment in the infrastructure and people we need to defend against malicious cyberattacks," Biden says.
Editors Scott Ferguson and Jeremy Kirk contributed to this story.