COVID-19 , Cyberwarfare / Nation-State Attacks , Forensics
Lazarus Group Targeted COVID-19 Research
Kaspersky: North Korean APT Group Used Malware in Attempt to Steal Information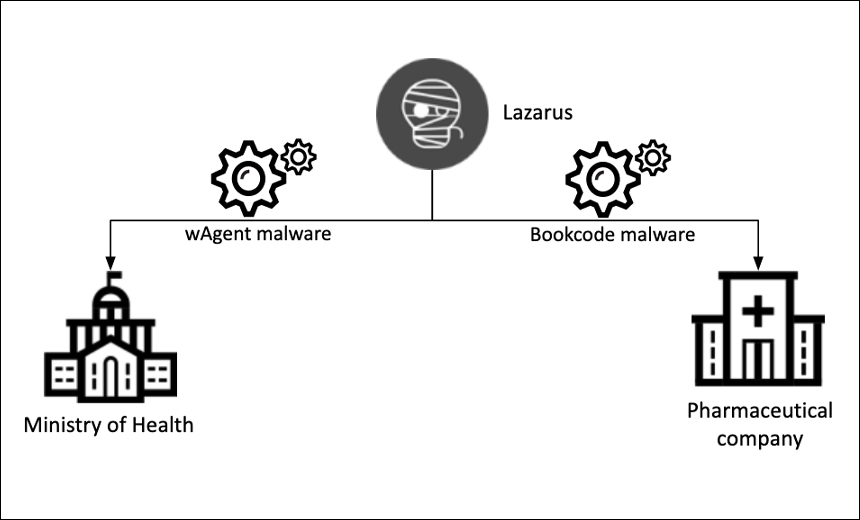
The Lazarus Group, a North Korean advanced persistent threat gang, apparently recently targeted a national ministry of health and a drug manufacturer involved in developing a COVID-19 vaccine in an attempt to steal information, according to the security firm Kaspersky.
See Also: 2023 Multifaceted Fraud Attacks Behavioral Biometrics as a Defensive Tool
In its report, Kaspersky does not identify the two organizations that were targeted with malware.
"While the group is mostly known for its financial activities, it is a good reminder that it can go after strategic research as well," says Seongsu Park, a security researcher at Kaspersky. "We believe that all entities currently involved in activities such as vaccine research or crisis handling should be on high alert for cyberattacks."
The unnamed ministry of health was hit with wAgent malware on Oct. 27, Kaspersky reports. This resulted in two Windows servers being compromised. Bookcode malware was used in the pharmaceutical company attack on Sept. 25. Kaspersky says both malware variants are tied to the Lazarus Group.
"Closer analysis found that the malware used against the Ministry of Health has the same infection scheme as Lazarus' previous attacks on cryptocurrency businesses," the researchers note.
Dissecting the Malware
Bookcode and wAgent have similar functionalities. Each has a backdoor that can enable attackers to gain full control of the victim's device, researchers say.
The wAgent malware used fake metadata to make it look like the legitimate compression utility XZ Utils, researchers note.
According to Kaspersky's telemetry, the malware was directly executed on the victim machine from the command line shell. It used a 16-byte string parameter as an AES key to decrypt an embedded payload – a Windows DLL. Once the embedded payload was loaded in memory, it decrypted configuration information using the decryption key.
Once the malware fetched the next payload from a command and control server, it was loaded directly into memory. The payload was a Windows DLL with backdoor functionalities.
"Using this in-memory backdoor, the malware operator executed numerous shell commands to gather victim information," the researchers note.
Bookcode
The Bookcode malware used to target the pharmaceutical company was previously spotted targeting a software company in South Korea, according to Kaspersky.
"We have also witnessed the Lazarus Group carry out spear-phishing or strategic website compromise in order to deliver Bookcode malware in the past," the researchers note. “However, we weren't able to identify the exact initial infection vector for this incident. The whole infection procedure confirmed by our telemetry is very similar to the one described in ESET’s latest publication on the subject."
Upon execution, the Bookcode malware read a configuration file and sent information about the victim’s device to the attacker's infrastructure. After successfully communicating to the C2 server, the malware provided backdoor functionalities.
"In the lateral movement phase, the malware operator used well-known methodologies. After acquiring account information, they connected to another host with the "net" command and executed a copied payload with the "wmic" command,” the researchers said. “Moreover, Lazarus used ADfind in order to collect additional information from the Active Directory. Using this utility, the threat actor extracted a list of the victim's users and computers.”
Lazarus Group’s History
The Lazarus Group allegedly has been involved in several thefts from banks and cryptocurrency exchanges, including the theft of $81 million from Bangladesh Bank in 2016.
A 2019 United Nation's report estimated the group had stolen about $571 million in cryptocurrency between 2017 and 2018 by targeting five exchanges in Asia. The Lazarus Group is allegedly providing money to the North Korean government (see: UN Report: N. Korea Targets Cryptocurrency Exchanges, Banks).