Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development
Chinese Hackers Use Fresh Trojan for Espionage
Proofpoint: 'Sepulcher' RAT Targets European Officials, Tibetan Dissidents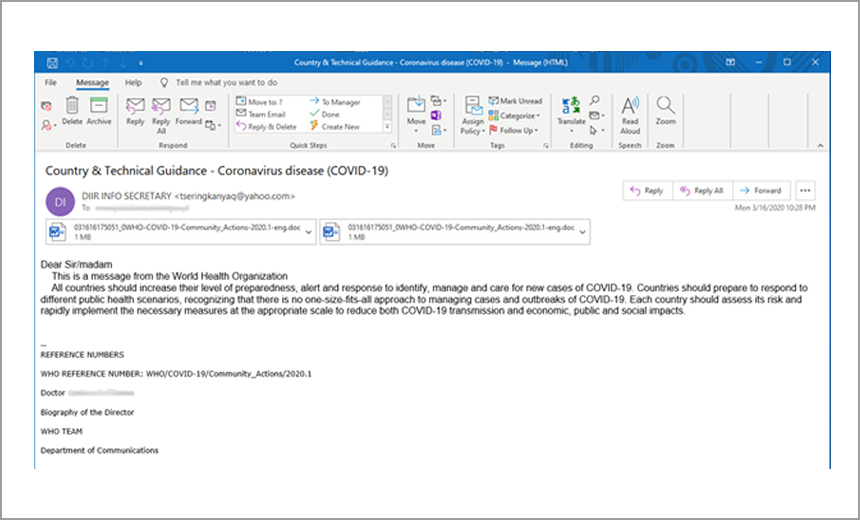
Proofpoint reports that a Chinese hacking group targeted European organizations, as well as Tibetan dissidents, with a new remote access Trojan called "Sepulcher” as part of a cyberespionage campaign.
See Also: 2019 Crowdstrike Falcon OverWatch Report (Japanese Language)
Once installed within a compromised device, the Trojan can obtain information about the infected host's drives, file information, directory statistics, directory paths, directory content, running processes and services, Proofpoint says in its new report.
The Sepulcher Trojan also can delete files and services as well as execute commands within infected devices.
The hackers deploying the Trojan used carefully crafted phishing emails to help deliver the malware to unsuspecting victims, according to Proofpoint. This included the use of messages that appear to come from the World Health Organization and contain details about the COVID-19 pandemic.
"Based on our analysis, Sepulcher contains basic remote access Trojan functionality, such as command shell access, scouting functionalities and gathering information about the resources on the infected machine," Sherrod DeGrippo, senior director of threat research and detection at Proofpoint, tells Information Security Media Group. "We note in our research that the RAT was not particularly novel. However, the pairing with timely social engineering lures demonstrate the actor leveraging global events to make up for their fairly pedestrian toolset."
Two Campaigns
The Sepulcher Trojan originated with a Chinese advanced persistent threat group known as TA413, according to Proofpoint. The attacks leveraging the Trojan came in two separate waves earlier this year.
The first wave, which started in March, targeted European organizations, including economic, diplomatic and legislative entities, according to the report. These emails, which used COVID-19 as a lure, likely were a starting point to gather information about economic conditions on the continent just after the pandemic started.
"This campaign’s specific focus on European economic, diplomatic, and legislative entities belies a possible momentary realignment for Chinese cyber espionage groups to collect information on global economies cast into upheaval as a result of COVID-19," according to the Proofpoint report.
The phishing emails sent to the European targets contained a malicious rich text format file called "Covdi.rtf" attached to the message. If opened, malicious code took advantage of a flaw in Microsoft's Equation Editor and installed a RTF object within a Windows file, according to the report. This enabled the hackers to deliver the Sepulcher Trojan to the compromised device.
The second wave of phishing emails, which started in July, focused on sending malicious messages to Tibetan dissidents and groups associated with Tibet, according to the report. The emails were designed to appear as though they came from a group called the "Women's Association Tibetan."
These phishing emails contained a malicious PowerPoint document attached to the message titled: "Tibetans Being Hit By Deadly Virus That Carries A Gun and Speaks Chinese," according to the report. If the document was opened, malicious code was enabled, which called out to a specific IP address to download and install the malware within a compromised device.
Focus on Tibet
TA413, which has been around since at least 2012, has used phishing emails and other lures to deliver malware, including Trojans called "LuckyCat" and "ExileRat."
Proofpoint found that the phishing emails used in the two most recent campaigns came from the same sending address associated with previous attacks attributed to TA413.
"Campaigns related to this group have been around for at least a decade with the recycled sender emails dating back to campaigns from 2012," DeGrippo says.
The group targeted Europe for the first time this year, most likely to gather intelligence on specific targets and take advantage of some of the confusion related to COVID-19, he explains.
"The observed activity targeting European economic, legislative and policy groups discussed in this research took place in March," DeGrippo says. "Since then, the actors appear to have pivoted back to their usual targeting of the Tibetan diaspora, which continued through July 2020. Based on the over 10-year focus of this APT on the Tibetan community, it is likely that those campaigns will continue."