Application Security , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime
Chinese APT Group Reportedly Develops Custom Backdoor
SharpPanda Backdoor Targets Southeast Asian Governments, Researchers Say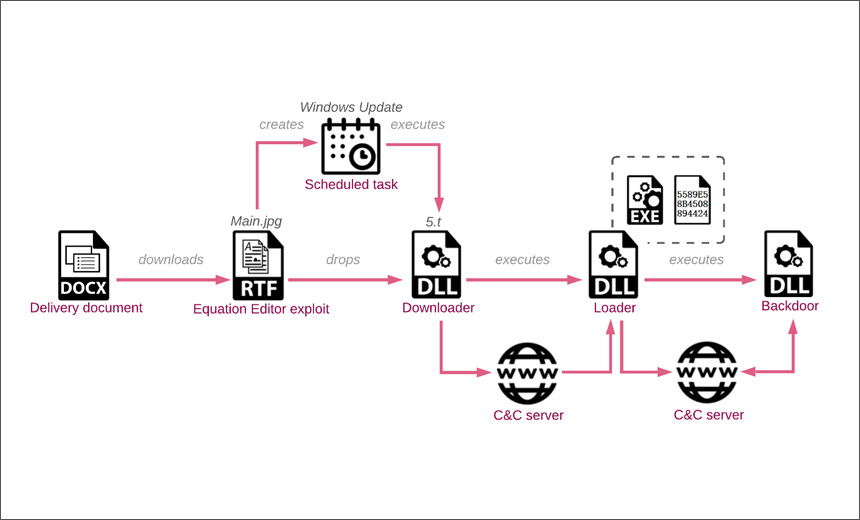
Check Point researchers have uncovered an ongoing campaign by a Chinese advanced persistent threat group that has spent the last three years testing and refining a custom backdoor in its arsenal to conduct espionage campaigns targeting governments in Southeast Asia.
See Also: Bank on Seeing More Targeted Attacks on Financial Services
The group, dubbed SharpPanda, uses spear-phishing attacks to gain initial access and leverage old Microsoft Office vulnerabilities together with a chain of in-memory loaders to attempt to install a previously unknown backdoor on victims’ machines.
Researchers note that the first stage of the infection chain's command-and-control servers is hosted by two different cloud services, located in Asia, in Hong Kong and Malaysia. The backdoor command-and-control server is hosted on Zenlayer, a U.S.-based provider that is widely used by multiple threat actors for command-and-control purposes.
"The threat actor operates the C2 servers in a limited daily window, making it harder to gain access to the advanced parts of the infection chain. Specifically, it returned the next stage payloads only during 01:00 - 08:00 UTC on workdays," researchers say.
Attack Analysis
During the investigation, researchers found that the campaign starts with a spear-phishing email containing malicious DOCX documents, which is sent to different employees of a government entity in Southeast Asia.
"In some cases, the emails are spoofed to look like they were from other government-related entities. The attachments to these emails are weaponized copies of legitimate looking official documents and use the remote template technique to pull the next stage from the attacker’s server," researchers note.
The document then delivers a rich text file that is weaponized with what Check Point calls the RoyalRoad exploit builder, which takes advantage of users who have failed to patch older vulnerabilities in Microsoft Word’s Equation Editor.
Once the victim access the file, the RoyalRoad payload plants another file in the infected device, which acts as a loader. On execution of the document, it launches the command-and-control server payload. The bootloader steals and transmits system information to a remote server, which then sends a shellcode downloader.
During the final stage of the infection chain, the malicious loader can download, decrypt and load a Dynamic Link Library file into memory. "In theory, this plug-in architecture might be used to download and install any other module in addition to the backdoor we received. The backdoor module appears to be a custom and unique malware with the internal name VictoryDll_x86.dll," researchers note.
The backdoor capabilities include the ability to delete, create, rename, read/ write files and get files attributes; get processes and services information; get screenshots; and get the victim’s computer information, including computer name, user name, gateway address, adapter data, Windows version (major/minor version and build number) and type of user and ability to shut down PC.
Check Point researchers attribute this attack to the Chinese cybercriminal group SharpPanda, on the basis of test versions of the backdoor from 2018 spotted uploaded in VirusTotal from China, as well as the use of the Royal Road RTF exploit tool. Upon further examination of the files, they were found to be older test versions of VictoryDll backdoor and its loaders chain.
Patched Exploit Still Used by Attackers
Microsoft issued a patch for the Equation Editor vulnerability in 2017 (see: Windows 10 Security Feature Broken, CERT/CC Warns), but security researchers continue to see the exploit used in various attacks, with a significant increase recently. "Despite the fact that these vulnerabilities are a few years old, they are still used by multiple attack groups, and are especially popular with Chinese APT groups," researchers note.
For example, Cisco Talos researchers wrote about a series of cyberattacks called "Frankenstein," The name refers to the attackers piecing together several different and unrelated open-source components as part of the campaign. The attackers targeted victims using malicious documents that took advantage of the CVE-2017-11882 exploit.