Cybercrime , Cybercrime as-a-service , Fraud Management & Cybercrime
China Hacking Underground Shows Rising Prowess
New Report Reveals New Malware, New Threats, New Threat Actors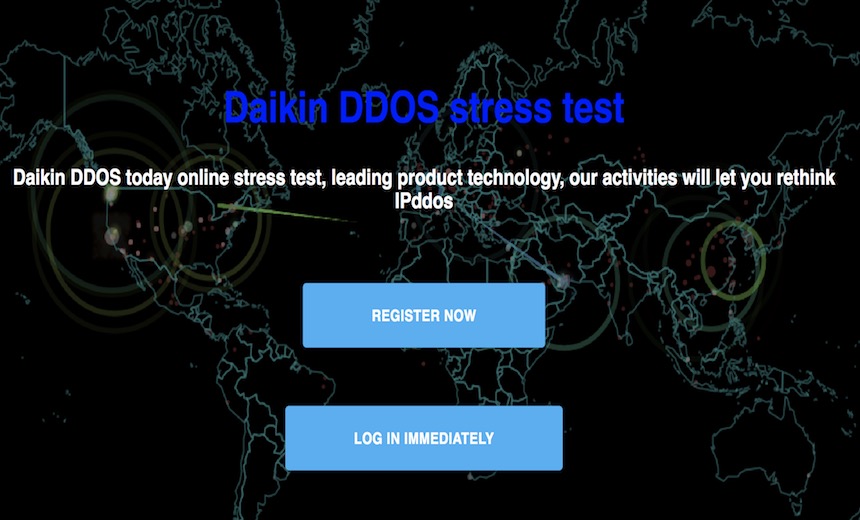
Much of the attention around Chinese hacking is directed toward the so-called advanced threat groups suspected to have links to the country's government.
But a new report shows that China's hacking goes far deeper, and there's a thriving scene of carders, drug dealers and malware writers that have adapted to an internet that's heavily controlled by the government.
The hacking forums give a preview of the next generation of Chinese hackers, says Itay Kozuch, director of threat research for the New York-based cybersecurity company IntSights. Kozuch is scheduled to speak at the Black Hat security conference in Last Vegas on Thursday.
"This is scary because these websites were not known," Kozuch says. "New malware, new threats, new threat actors."
China's Underground Scene
IntSights studied the hacking scenes of China and other Asian countries, including Japan, South Korea, Indonesia and Vietnam, for six months, compiling the key findings in its report. Analyzing hacking scenes in Asia is difficult due to language barriers and unfamiliarity with local hacker protocols.
"Finding cyber threat hunters who are fluent in the local language is a challenge alone," according to IntSights' report. "However, threat hunters also need to be intimately familiar with the dark web slang and rules of engagement of that region, so they can effectively blend in and perform reconnaissance."
Much of the report is dedicated to China, which in many respects has taken away or made it more difficult to use common tools of the trade. For example, China blocks the Tor network, which provides greater anonymity when browsing the web by encrypting browsing traffic through a worldwide network of nodes.
Tor can also be employed to create so-called "hidden" websites, whose true domain name is replaced with a ".onion" suffix. Onion sites can only be called upon using the Tor browser.
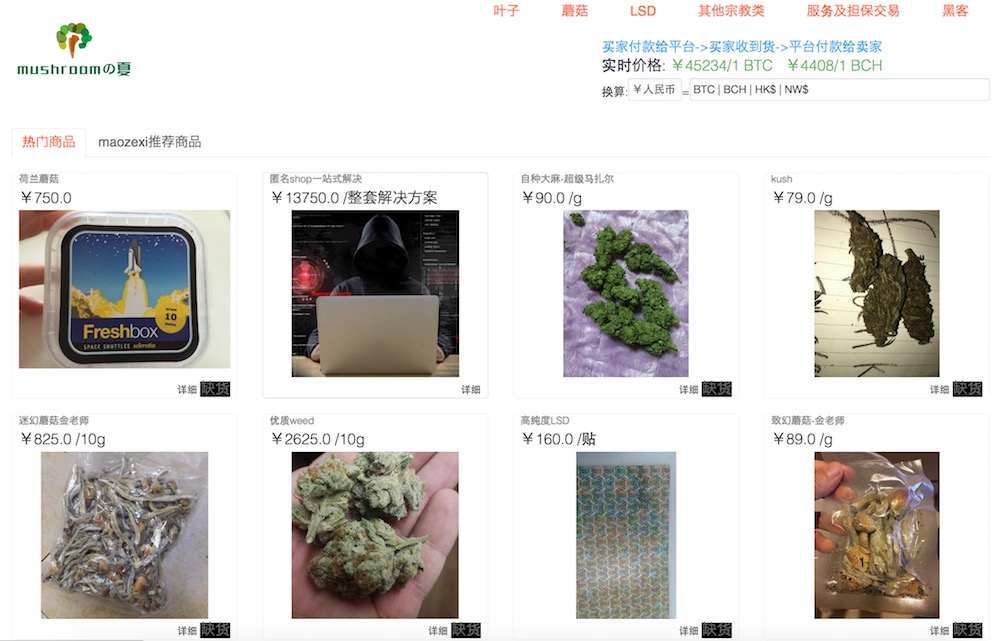
Hidden sites have been favored by those running underground markets for illegal goods due to the difficulty in investigating their operators. As a result, many of the Chinese hacking sites for those offering illegal goods are simply on the clear web, Kozuch says. That allows for higher profits and greater access to customers.
Banned: Bitcoin, VPNs
Cryptocurrency such as bitcoin is also banned in China. But it's not the illegality that dissuades people who are already engaged in cybercriminal activity away from bitcoin, but rather a market problem.
Bitcoin and other cryptocurrencies are difficult for buyers to obtain, so goods instead are priced in Chinese yuan, Kozuch says. Payments are made through normal bank transfers, he adds.
China has also cracked down on VPNs. The country banned VPNs not approved by the government on March 31. VPNs were used to skirt China's censoring of websites and content, including major services such as Facebook and Twitter.
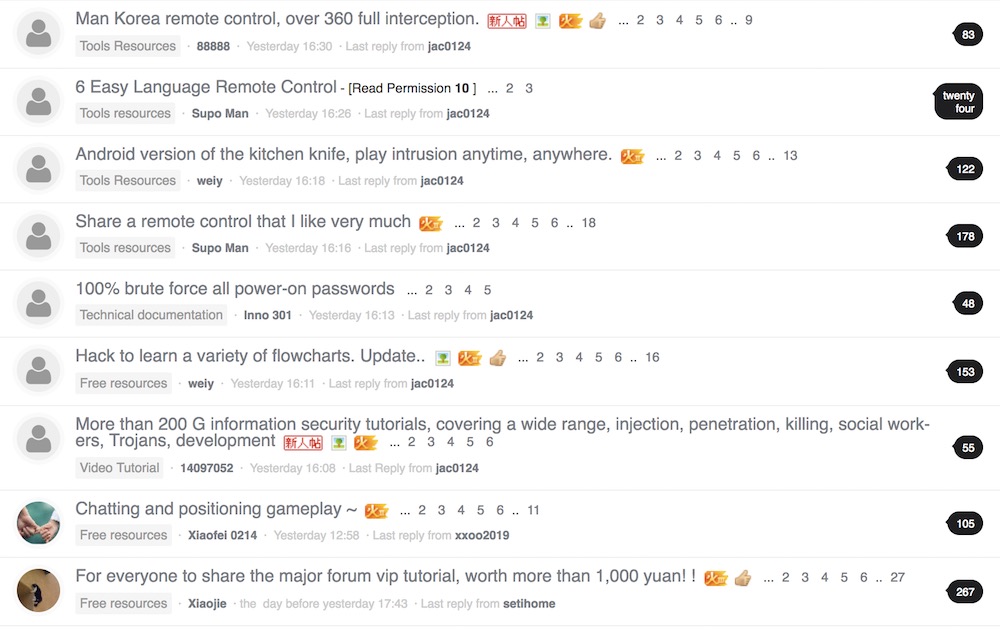
The goods offered on Chinese hacking forums mirror those on English-speaking ones: drugs, forged documents, stolen personal data, data from breaches and details of bank accounts and credit cards.
Chinese forums also offer a menu of malware, exploits and hacking tools, including some that Kozuch says have never been seen before. Chinese hackers apparently don't recycle as much malware as those in Western countries, he says.
But it's difficult to gain the trust of those participating in forums in order to obtain samples. "It's hard to buy malware, especially if you are not located in China, but we are working on it," Kozuch says.
More Research Needed
Services offering for-hire distributed denial-of-service attacks are also available in China. One such service found by IntSights advertised an attack stream of 500 Gbps, which is fairly heavy firepower for a DDoS attack. It costs about US$730 per month for what the advertisement says is "unlimited attacks."
That type of capability "means you have a lot of infrastructure, and you've probably done it before," Kozuch says.
"There is a lot that we are not covering and still needs to be found. It's a whole new world that we need to invest a lot of work in to crack it."
—Itay Kozuch, IntSights
Other goods on underground markets are disturbing. In a grisly finding, IntSights found a few dark Chinese web forums and Telegram channels "who offered human organs for sale," the report says.
But in six months of research, Kozuch says the company has only scratched the surface of the some of the communities.
"There is a lot that we are not covering and still needs to be found," he says. "It's a whole new world that we need to invest a lot of work in to crack it."