Account Takeover Fraud , Cybercrime , Fraud Management & Cybercrime
Card Skimmer Found Hitting Vulnerable E-Commerce Sites
Malware Specifically Targets Sites Running Unsupported ASP.NET Software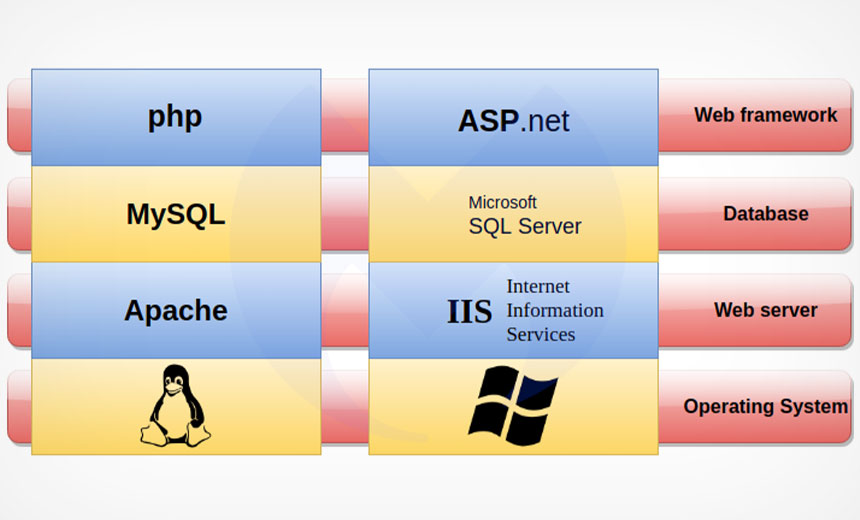
A credit card skimmer that has been operating since April is specifically targeting sites hosted on Microsoft IIS servers that are currently running an out-of-date version of ASP.NET, according to security firm Malwarebytes.
This approach differs from most credit card skimming attacks that target sites built on the widely adopted Linux, Apache, MySQL and PHP (LAMP) stack, Jerome Segura, Malwarebytes' director of threat intelligence, notes in the report published this week. Specifically targeted were sites running ASP.NET version 4.0.30319 which has reached end-of-life and is no longer supported and therefore has many vulnerabilities .
About 27 million websites are currently run on ASP.NET 4.x, but Malwarebytes only found a few being attacked.
"The credit card skimming landscape is busy with a number of threat actors which end up competing with one another on the same victim sites. It's possible this group decided to go after less obvious targets and hoped to fly under the radar from defenders who also happen to focus on Magento and other popular e-commerce platforms," Segura tells Information Media Security Group.
Potential Pool of Targets
Despite the large pool of potential targets, Malwarebytes has only been able to identify a few victims.
"We found over a dozen websites that range from sports organizations, health, and community associations to (oddly enough) a credit union. They have been compromised with malicious code injected into one of their existing JavaScript libraries," Segura says.
Some historical evidence of other victims who have been hit in the past was uncovered as part of his research, he says, but they have since been remediated. The total number of targets number is not available.
The skimmer steals payment card numbers and tries to also swipe passwords, although the latter activity is not correctly implemented and does not always work, according to Malwarebytes.
Segura says the skimmer is not that different from others currently operating in how it collects and exfiltrates data. The novelty is that it was only found on ASP.NET websites.
"The skimmer is embedded in an existing JavaScript library used by a victim site. There are variations on how the code is structured but overall, it performs the same action of contacting remote domains belonging to the threat actor," Segura says.
One area Malwarebytes was unable to nail down is the threat actor's identity. As of now, it's unknown if this is a new group, but based on an examination of the code it appears the group has previously performed skimming operations.
Skimmers in the News
Other skimmer variants have also been busy with the hacking group known as "Keeper" being found using Magecart-like web skimmers to target the online checkout sites and portals of hundreds of e-commerce sites in order to steal the payment card data from about 184,000 customers, according to Gemini Advisory (see: 'Keeper' Group Targeted Payment Card Data on 570 Sites).
This week the Dutch security firm Sansec published a report tying the infrastructure used by some Magecart groups to the North Korean hackers known as Lazarus or Hidden Cobra (see: North Korean Hacking Infrastructure Tied to Magecart Hits).