3rd Party Risk Management , Business Continuity Management / Disaster Recovery , Critical Infrastructure Security
Alert: 'Cuba' Ransomware Slams Critical Sector Organizations
$43.9 Million in Ransom Payments Extorted by Attackers in Latest Campaign, FBI Warns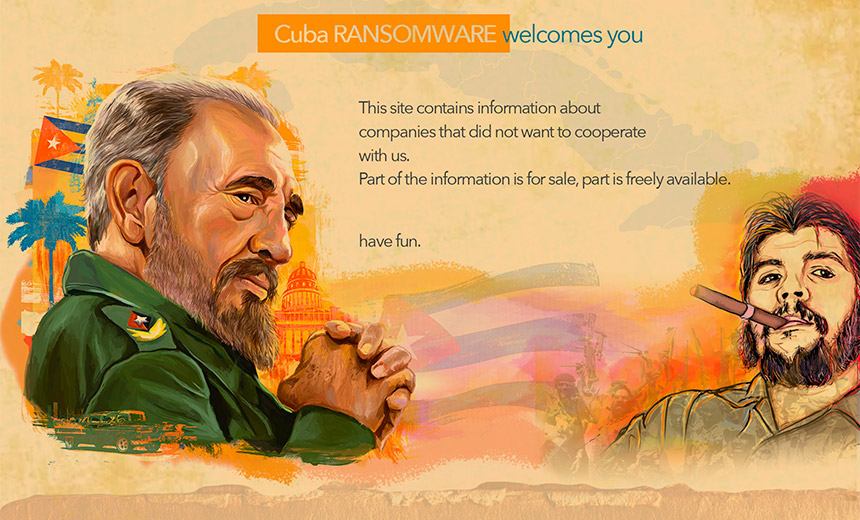
The FBI is warning that the "Cuba" ransomware group has managed to extort $43.9 million in ransom payments from victims after compromising at least 49 entities across five critical infrastructure sectors.
See Also: Ransomware Response Essential: Fixing Initial Access Vector
The bureau's Friday flash alert says that the ransomware group has targeted critical national infrastructure organizations including the financial, government, healthcare, manufacturing and IT sectors since early November.
"Cuba ransomware actors have demanded at least $74 million and received at least $43.9 million in ransom payments," the alert states. The operation is not believed to have any ties with the eponymous country or its government.
Hancitor Malware
The FBI says that Cuba ransomware is distributed through Hancitor malware, a loader known for dropping or executing stealers, such as remote access Trojans and other types of ransomware, onto victims' networks.
In May, security firm Group-IB found instances of attackers using the Hancitor malware downloader to deliver Cuba ransomware as part of an email spam campaign for data exfiltration and ransom extortion (see: Malspam Campaign Used Hancitor to Download Cuba Ransomware).
Group-IB says that the ransomware gang used Hancitor to help gain access to targeted networks, spreading the malware in malicious email attachments disguised to look like DocuSign notifications. Once a victim's device had been compromised, the campaign operators then used Cuba ransomware's dedicated data leak site to publish the exfiltrated data if its ransom demands were not met.
It's unclear when the campaign began or who the victims are. But as of late April, Group-IB researchers reported the site had listed the data of nine companies, primarily from aviation, financial, education and manufacturing industries in the U.S. and Europe.
The FBI's latest alert states that the Hancitor malware-wielding attackers use phishing emails, Microsoft Exchange vulnerabilities, compromised credentials or legitimate remote desktop protocol tools to gain initial access to a victim's network.
"Cuba ransomware actors use legitimate Windows services - such as PowerShell, PsExec, and other unspecified services - and then leverage Windows Admin privileges to execute their ransomware and other processes remotely," according to the FBI alert.
The alert further states that the Cuba ransomware actors compromise a victim's network through the encryption of target files with the ".cuba" extension (see: 'Cuba' Ransomware Gang Hits Payment Processor, Steals Data).
Technical Details
The FBI says that once a victim's system is compromised, the ransomware operators install and execute a "CobaltStrike beacon as a service on the victim's network via PowerShell."
Upon successful installation, the ransomware downloads two executable files, which include "pones.exe" for password acquisition and "krots.exe," which enables Cuba ransomware operators to write to the compromised system's temporary, or .tmp, file.
"Once the TMP file is uploaded, the 'krots.exe' file is deleted and the TMP file is executed in the compromised network. The TMP file includes application programming interface calls related to memory injection that, once executed, deletes itself from the system. Upon deletion of the TMP file, the compromised network begins communicating with a reported malware repository located at Montenegro-based Uniform Resource Locator (URL) teoresp.com," the FBI adds.
Cuba ransomware attackers also use the Mimikatz credential-stealing software together with RDP to log into compromised network hosts, the FBI says. After making a successful RDP connection, the attackers sometimes also use CobaltStrike penetration testing tools to gain deeper access to a victim's network, backed by PowerShell scripts to better automate the attack.
"One of the initial PowerShell script functions allocates memory space to run a base64-encoded payload. Once this payload is loaded into memory, it can be used to reach the remote command-and-control - C2 - server and then deploy the next stage of files for the ransomware," the FBI says. "The remote C2 server is located at the malicious URL kurvalarva.com."
Mitigation Measures
The FBI alert lists several recommended steps for preventing and recovering from ransomware incidents. Those include regularly backing up data, implementing multifactor authentication and maintaining offline backups of data.
Also, organizations should ensure all operating systems and software are up to date, and they should remove unnecessary access to administrative shares.
Other essential defenses include implementing network segmentation, having a recovery plan to maintain and retain multiple copies of sensitive or proprietary data, and locating servers in a physically separate, segmented, secure location.
Organizations should also install updates and patch operating systems, software and firmware as soon as updates are released, the FBI says.
The FBI is encouraging organizations to share information boundary logs showing communication to and from foreign IP addresses, bitcoin wallet information, the decryptor file, and any benign samples of encrypted files.
The FBI reiterated in its alert that it recommends organizations do not pay ransoms because payment does not guarantee files will be recovered and also emboldens cybercriminals to wage further attacks or encourage other criminal actors to engage in the illicit activities.
"However, the FBI understands that when victims are faced with an inability to function, all options are evaluated to protect shareholders, employees and customers," the bureau states. "Regardless of whether you or your organization have decided to pay the ransom, the FBI urges you to promptly report ransomware incidents to your local field office."
Past Attacks
Attackers have used Hancitor downloader and Cuba ransomware to target several victims in previous campaigns.
In February, Cuba ransomware hit a Seattle-based billing and payment processing provider used by organizations and government agencies across California and Washington (see: 'Cuba' Ransomware Gang Hits Payment Processor, Steals Data).
In 2019, a report by security firm Malwarebytes found hackers were deploying Emotet, Hancitor and Trickbot as part of a malicious spam campaign (see: Emotet Malware Returns to Work After Holiday Break).
And in 2017, two security researchers found that a 2016 energy blackout in Ukraine was initially caused by a spear-phishing attack that deployed Hancitor. The researchers found the hackers used Hancitor to install additional attack code on infected systems and that it had undergone 500 iterations two weeks before it was deployed (see: Ukraine Blackout Redux: Hacking Confirmed).