Breach Notification , Cybercrime , Cybercrime as-a-service
Accenture: Ransomware Attack Breached Proprietary Data
Consultancy Discloses Data Leak Tied to Attack For Which LockBit 2.0 Claimed Credit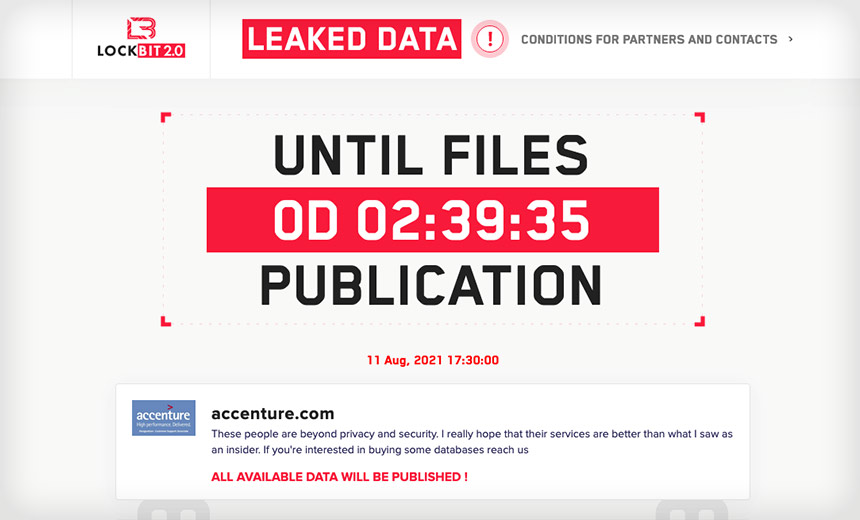
The consultancy Accenture has confirmed that "irregular activity" in its IT networks last quarter, which it disclosed in August, also resulted in a breach of sensitive information.
See Also: Ransomware Response Essential: Fixing Initial Access Vector
Dublin-based Accenture disclosed the data breach on Friday in its annual report for its fiscal year ending Aug. 31, which it filed as a form 10-K to the U.S. Securities and Exchange Commission, as Bleeping Computer first reported.
"In the past, we have experienced, and in the future, we may again experience, data security incidents resulting from unauthorized access to our and our service providers' systems and unauthorized acquisition of our data and our clients' data including: inadvertent disclosure, misconfiguration of systems, phishing, ransomware or malware attacks," Accenture says in the filing.
"For example, as previously reported, during the fourth quarter of fiscal 2021, we identified irregular activity in one of our environments, which included the extraction of proprietary information by a third party, some of which was made available to the public by the third party."
Accenture first confirmed on Aug. 11 that it had fallen victim to an attack, but declined to offer any additional details.
"Through our security controls and protocols, we identified irregular activity in one of our environments," the company told Information Security Media Group at the time. "We immediately contained the matter and isolated the affected servers. We fully restored our affected systems from backup."
The company added: "There was no impact on Accenture's operations, or on our clients' systems."
According to the company's annual report, the initial attack occurred sometime between June and August.
LockBit 2.0 Takes Credit
The LockBit 2.0 ransomware-as-a-service operation claimed credit for the attack, listing Accenture on its data-leak site as a victim and threatening to leak stolen data unless the consultancy paid a ransom. This is a common tactic used by ransomware groups that have data-leak sites, to pressure victims into paying a ransom, or else serve as a warning to future victims that unless they pay, their stolen information will get dumped online.
But security experts caution that while many groups claim to have stolen data, or to have stolen sensitive information in particular, attackers often lie, and may either have stolen nothing of value, or nothing at all.
Stolen Data Got Dumped
Accenture appears to have declined to pay its attackers anything, leading to all of the stolen data eventually getting dumped.
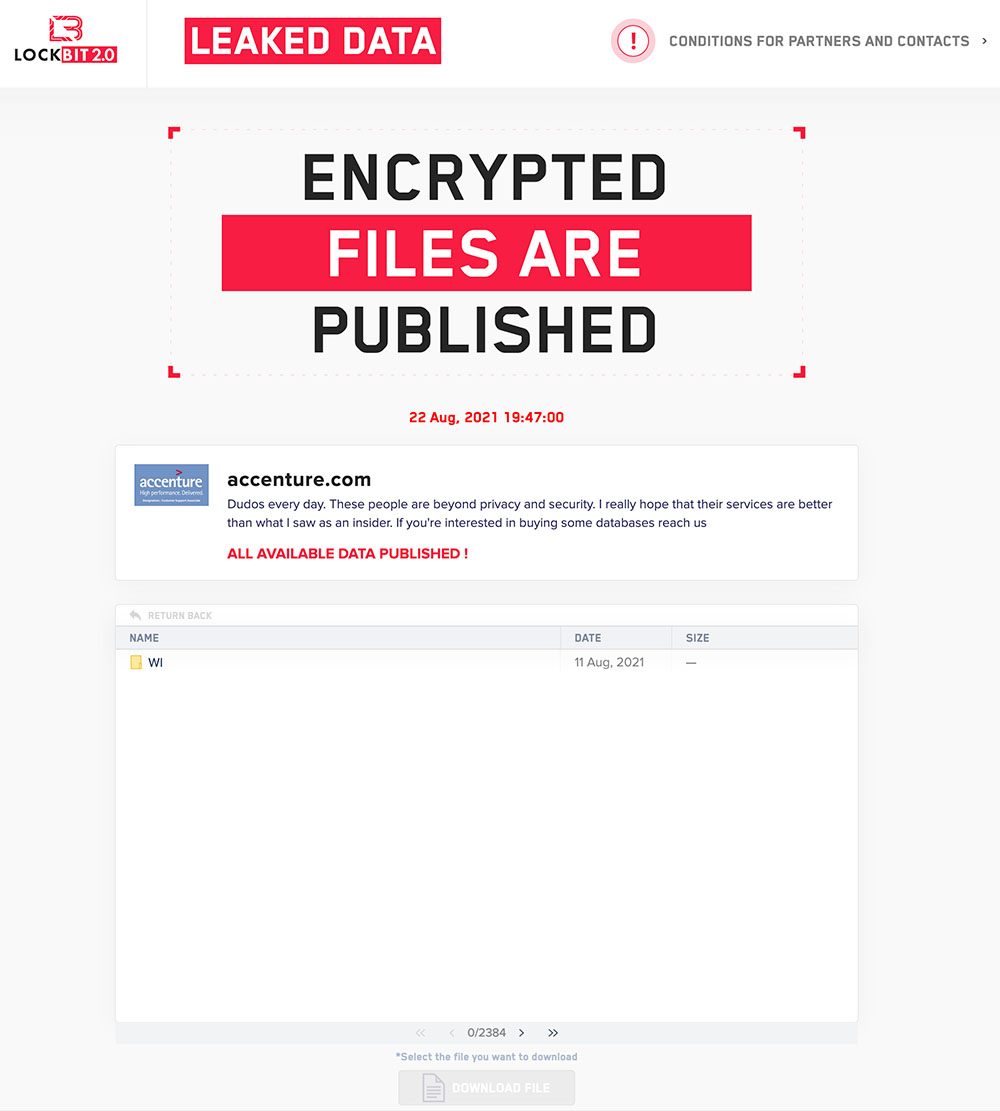
On its leak site, LockBit now lists for download 2,384 directories - which security experts say included even more subdirectories - as having been stolen from Accenture. By Aug. 22, the group had finished leaking the stolen data for free download from its data-leak site. "If you're interested in buying some databases reach us," the site reads.
In August, a CNBC reporter said that a review of the leaked Accenture data found what appeared "to be PowerPoints, case studies, quotes and the like." Accenture declined to comment about whether it directly notified any individuals or customers about the breach, for example, if their employees' personal details might have been exposed, or other information stolen pertaining to business partners or customers. Instead, the company referred again to the statement it issued in August.
Israeli threat intelligence firm Kela says consultancies are amongst the types of organizations most targeted by ransomware attackers. While not all victims publicly come to light, of the attacks it's tracked over the last month by victims being named via data-leak sites, Kela says these are the top sectors being targeted:
- Manufacturing and industrial products: 18% of all reported ransomware attacks;
- Professional services: 16%;
- Engineering and construction: 8%;
- Technology: 8%;
- Consumer and retail: 7%.
LockBit Keep Recruiting
LockBit is run as a ransomware-as-a-service operation, which means the core administrators develop and maintain the malware and data-leak portal. Pre-vetted affiliates take the ransomware, infect victims and share in any resulting profits.
LockBit has continued to post numerous new victims in recent weeks, including a computer system design firm in New Jersey, an Idaho regional transit organization, corporate law firms in Australia and New Jersey, and a Latin American business processing outsourcing firm, among others.
LockBit's administrators continue to aggressively market their ransomware to prospective affiliates, emphasizing the speed with which their malware crypto-lock systems - claiming that no one has yet been able to forcibly break that encryption - and talking up the malware's ability to spread itself inside targeted networks (see: 9 Takeaways: LockBit 2.0 Ransomware Rep 'Tells All').
Perhaps unsurprisingly, the group says it is keen to recruit affiliates with relatively advanced skills with red-team software. "We cooperate only with experienced pentesters who are real professionals in such tools as Metasploit Framework and Cobalt Strike," LockBit says in an advertisement for new affiliates posted on its data-leak site. "With our help you can easily get more targets over the weekend than with any other affiliate program over the week."
LockBit says affiliates set ransom demands. "Only you decide during communication how much the encrypted company will pay you," its advertisement says. "You get the payment to your personal ewallets in any currency, after which you transfer us the percentage of the foreclosure amount."
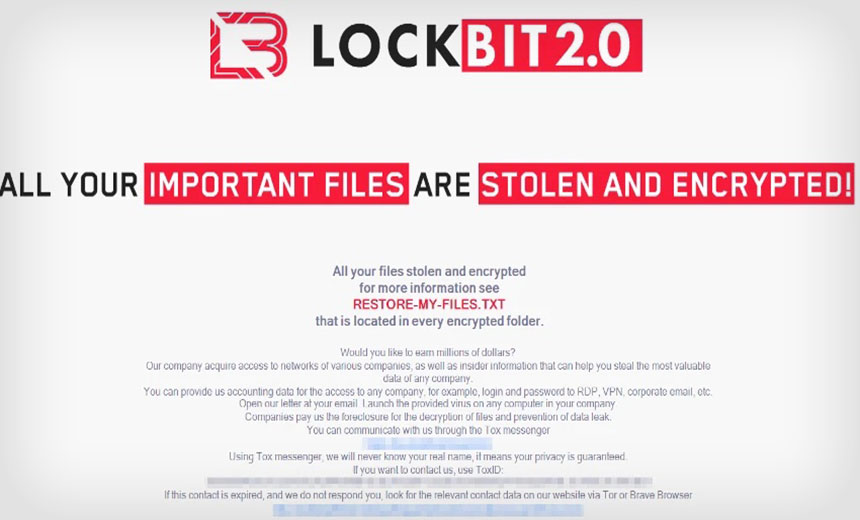
The group does list multiple caveats that won't come as a surprise to any experienced affiliates, the principle one being: "LockBit 2.0 does not function in post-Soviet countries." This is a typical restriction for Russian-speaking ransomware groups, which remain keen to avoid running afoul of local authorities.